Phishing is when criminals use fake emails to lure you into clicking on them and handing over personal information, sending them money, or installing malware on your device. It’s fairly easy to avoid a scam email when you know what to look for.
Here are some common characteristics of phishing messages:
- Contains an offer that’s too good to be true
- Language that’s urgent, alarming, or threatening
- Poorly-crafted writing with misspellings and bad grammar
- Greetings that are ambiguous or very generic
- Requests to send personal information
- Requests for gift cards or money transfers
- Urgency to click on an unfamiliar and unexpected hyperlink or attachment
- Strange or abrupt business requests
- Sender e-mail address doesn’t match the company it’s coming from
When you identify a real or simulated phishing message you should report it using the “Report phishing” feature in Gmail. When you report phishing in this way, you help train Google’s phishing detection algorithm. Also, ITS staff are notified immediately and directly. These notifications contain all the information required to conduct an investigation and take appropriate actions. These actions can include deleting phishing messages from other inboxes, blocking the sender, warning people who may have engaged with the scammer, or reporting the account to the service provider. For more detail on how to report phishing, check out 1 Minute on How to Report Phishing.
Get Trained.
October is when we publish new web-based cybersecurity training for faculty, staff, and students. This training is required annually for ALL faculty and staff. Students are welcome to check it out, too. Thanks to everyone who has completed this training so far. Those who have not yet completed this training have until November 1 to do so.
Cybersecurity Annual Training for Employees 2022-2023
Student Cybersecurity Training
Phishing Simulation.
Last week we conducted a phishing simulation exercise — that is, we phished ourselves. This was a learning experience that allowed everyone to practice identifying and responding to a suspicious message.
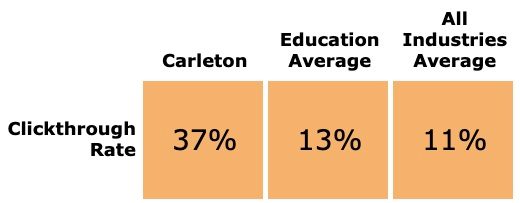
The average clickthrough rate for education institutions is 11% and for all industries is 13%. We want to have a lower number than one or both of these figures. Our clickthrough rate was 36% — so, this message was particularly convincing for many. We will have another opportunity to practice soon. We will have a similar exercise next month.
On the upside, our phishing reporting rate was 16%, which exceeds both the average for education organizations (6%) and the average across all industries (13%). (In this case, a higher number is better.)
The message template we used resembled real phishing messages we receive regularly—specifically, abuse of file sharing, digital signature, and billing services (ex. Google Drive, One Drive, Dropbox, AdobeSign, Docusign, Paypal and Quickbooks). These messages look real because they are genuine notifications coming from actual services.
When you receive messages like these, ask yourself:
- Does the user’s email address match the person who is supposedly sending the message?
- Am I expecting this kind of message from this person?
These are the same kinds of things that would have been good to ask regarding our simulation message. For more detail on how you would have known our simulated message was bogus, check out this graphic.
Cybersecurity Town Hall: The Life-Changing Magic of Cybering Up
Mark your calendar. I’ll be hosting a cybersecurity town hall on Oct 31st. This will be an informal informational session with Q&A. I’ll describe the current state of the higher education cyberthreat and the steps you can take to keep the campus and your own digital life secure. There will be ample time for discussion.
Date & Time: Noon, Monday, October 31, 2022.
Join Zoom Meeting:
https://carleton.zoom.us/j/97989435502?pwd=RE1MWCtaOWFCaUYxSVBMQWhsbUxnQT09
Meeting ID: 979 8943 5502
Passcode: 886246
You will need to use your Carleton or St. Olaf account to log in.
Cybersecurity is everyone’s job. Be safe out there and, if you ever have any questions, don’t hesitate to contact me or the Helpdesk.
